- SMS Authentication: This is the simplest form of MFA, where a verification code is sent to your mobile phone via SMS. However, this method could be more secure, as SMS messages can be intercepted or spoofed by cybercriminals.
- Authenticator App: This is a more secure method, installing an authenticator app on your phone that generates OTPs for you. The app works even when you don’t have an internet connection, and it can be used to authenticate multiple accounts.
- Hardware Token: This is a physical device that generates OTPs and is often used in high-security environments. However, hardware tokens can be expensive and difficult to manage.
- Biometric Authentication: This method uses your physical characteristics, such as your fingerprint or facial features, to verify your identity. Biometric authentication is highly secure, but it requires specialized hardware and software.
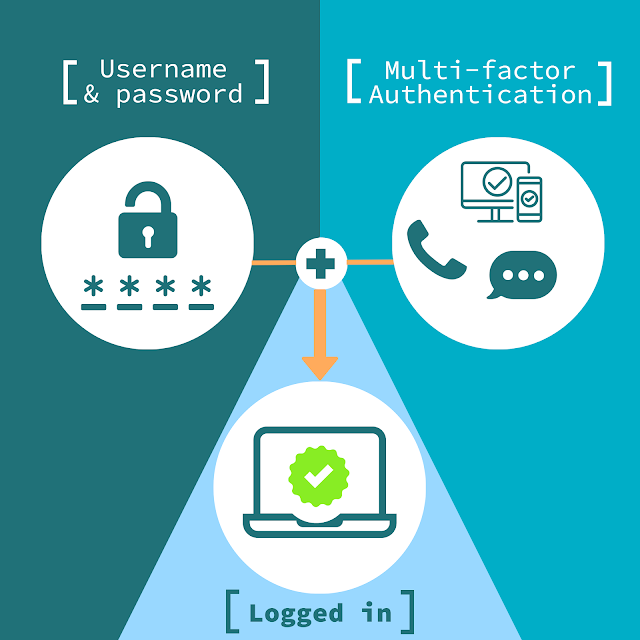
WEB AUTHENTICATION BY USING MFA
VOLUME 2
The most common and effective use of MFA is for web authentication. If a user wanted to access a web application, they’d experience a process such as this: navigate to a landing page, enter login credentials, and use an authentication code from Google Authenticator. Web applications that access internal databases and other sensitive information require a high level of security and would use a similar method. In addition to securing applications with MFA, security-conscious organizations should avoid credentials and use certificates. Certificates add an extra layer of security that further protects against hacking attacks and human error. When determining your security strategy for web applications, it is worth evaluating how many people use the application. If it is used by everyone in the organization, MFA may not be appropriate for the situation. The average cost per user is high for MFA, so if certificate-based authentication is enough to level of security, it may be a better option. Certificates and MFA used together are a strong security system but for widely used web applications.
Wi-Fi Authentication
If your network authenticates users with a RADIUS server, the technology to implement MFA does not exist. If it does become an option in the future, it would be difficult to justify using MFA for that purpose. The costs associated would be high, and the time-consuming user experience would be a common complaint. Entering multiple levels of authentication every time a user connects to the network would be a hassle and could lead to users browsing with personal data or on insecure networks.
For Wi-Fi authentication, a highly recommended option is the use of certificates with onboarding software. This allows users to configure their devices in minutes to be authenticated by the RADIUS, and they never have to enter credentials to get on the network. MFA could be a step in the certificate enrolment process. In this situation, a user’s identity would be confirmed by entering credentials and another form of authentication, such as biometrics. The process would be lengthened by one step, but the risk of someone stealing credentials and obtaining a certificate would be nearly zero. Although certificates cannot be stolen from a device, it’s important to train users about proper secure network usage. For example, if they do not lock their cell phone with a passcode, the certificate is insecure. If the device is stolen or lost, anyone could pick it up and instantly be connected to the network with no need to steal credentials. Technology goes a long way to secure your data, but you must ensure that those who use the network are trained to maintain security as well.
What puts MFA above traditional authentication is the difficulty a prospective thief would experience when trying to steal personalized data. If they manage to steal a set of credentials, they’ll be thwarted by a biometric scanner or authentication code. If used in combination with certificates, the network seamlessly authenticates users and negates over-the-air credential theft. Several combinations of this security type exist, and it has proven its effectiveness in protecting users and the network. And above all, properly training network users to follow secure protocols will maintain the integrity of the network in perpetuity.